Schneier on Security: A newly discovered piece of malware, Duqu, seems to be a precursor to the next Stuxnet-like worm and uses some of the same techniques as the original. Link to Source
Symantec: W32.Duqu: The Precursor to the Next Stuxnet
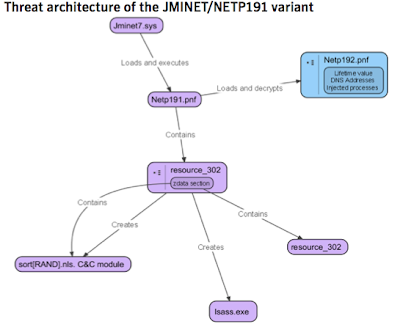
Duqu is essentially the precursor to a future Stuxnet-like attack. The threat was written by the same authors (or those that have access to the Stuxnet source code) and appears to have been created since the last Stuxnet file was recovered. Duqu’s purpose is to gather intelligence data and assets from entities, such as industrial control system manufacturers, in order to more easily conduct a future attack against another third party. The attackers are looking for information such as design documents that could help them mount a future attack on an industrial control facility. Read Full Article
F-Secure: Duqu – Stuxnet 2:
A new backdoor created by someone who had access to the source code of Stuxnet has been found.
Stuxnet source code is not out in-the-wild (only the binaries). Only the original authors have the source code. So, this new backdoorwas created by the same party that created Stuxnet. Read Full Article
Norman: W32/Duqu – Stuxnet lite?
Oct 18th, our competitor Symantec published an extensive report on a malware called Duqu, which appears to bear some resemblance to last year’s Stuxnet worm. This time the malware does not seem to be aimed at sabotage, but is instead made for intelligence gathering. Read Full Article
Wired: Son of Stuxnet Found in the Wild on Systems in Europe
Duqu, like Stuxnet, masks itself as legitimate code using a driver file signed with a valid digital certificate. The certificate belongs to a company headquartered in Taipei, Taiwan, which Symantec has declined to identify. F-Secure, a security firm based in Finland, has identified the Taipei company as C-Media Electronics Incorporation. The certificate was set to expire on August 2, 2012, but authorities revoked it on Oct. 14, shortly after Symantec began examining the malware. Read Full Article
Update, Oct 24, Added Avira Article too:
Avira: Stuxnet v2 or TR/Duqu
The Stuxnet virus has gone to the next generation: “TR/Duqu”.
Avira already detects the new malware since VDF 7.11.16.63, which was released on 2011-10-19. Read Full Article